Built for Beauty
Intuitive photo app for aesthetics
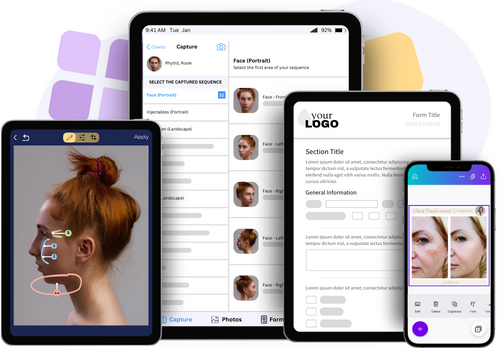
The RxPhoto app is specifically designed to help your med spa, wellness or plastic surgery practice demonstrate treatment success and showcase exceptional patient outcomes. Capture beautifully consistent before-and-after photos, then effortlessly store and manage them with other important client information. Effortlessly store, manage and showcase before-and-after photos to demonstrate treatment success and showcase your exceptional results.
Elevate Your Business by Working with
Market Leaders in Photo Technology
Perfection in Every Picture
High-quality imaging and editing tools
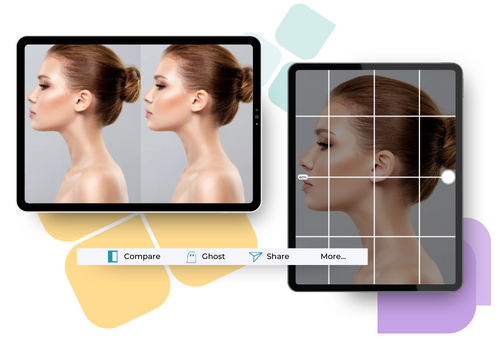
RxPhoto is the industry’s most powerful tool for showcasing aesthetic treatments and elective procedures. With advanced imaging and editing tools, RxPhoto captures precise, detailed photographs that support accurate diagnosis and treatment, enhancing the experience for both prospects and clients.

Increase patient trust and treatment acceptance rates through visual aids that help clients better understand their options.
RxPhoto eliminates the time and trouble of using cameras and downloading image after image into a patient’s record. Instead, you’ll capture high-quality, high-resolution, HIPAA-compliant digital photos with precision and clarity.
Digital intake and consent forms decrease the likelihood of misreading handwritten notes, helping to eliminate no-shows and reduce the cost and burden of using paper forms.
Great photos sell more services. Empower your customers with visual proof of progress and they’ll be more likely to return for further treatments.


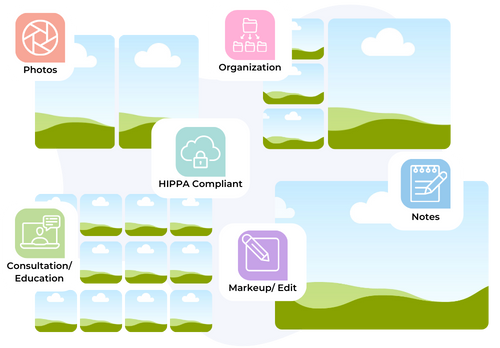
Robust Features
The industry leading photo tool
Utilize sliders, ghosting effects, and side-by-side comparisons to vividly showcase surgical or treatment outcomes and enhance client and prospect engagement.
Just Ask
Our Customers
Your Comprehensive Solution
Beyond photography, RxPhoto delivers a range of features tailored to meet the specific needs of elective and aesthetics practitioners. From treatment planning to compliance, RxPhoto empowers you to deliver exceptional care.
Integration

Treatment Planning

Compliance
